Cybersecurity for startups – recruit the good hackers
Recruiting good hackers who can test your startup’s technologies for hidden vulnerabilities is essential to ensure your startup has a solid security posture because implementing multiple security measures is not enough. These “good hackers” who are also known as ethical hackers emulate a malicious actor’s adversarial behaviors and search for weaknesses or vulnerabilities in your technologies to exploit them. These technologies include networks, systems, hardware, system infrastructure, or an entire organization. For example, they may perform penetration testing of your networks and identify weaknesses that a potential adversary could leverage. The purpose of an ethical hacker’s job is to help secure your startup from attackers before they get a chance to exploit the vulnerabilities.
!This article is a part of a series about cybersecurity advice for startups. The previous one covered logging best practices.
What is hacking?
Hacking is usually an act of technical methods or tactics and techniques that seek to compromise networks and endpoint devices, such as computers, laptops, tablets, mobile phones, etc. However, hacking may also involve using psychology to trick a victim into clicking on a phishing link, such as in social engineering. Thus, an individual who performs the act of hacking is a hacker.

The hacker mindset
In an interview with Hacking Is NOT a Crime’s Phillip Wylie, a penetration tester, educator, and author, he shared the origins of the term hacker. Phillip Wylie stated,
The original term for “hacker” was related to programming, inventors, and people who could take out devices and enhance those capabilities. People like Steve Wozniak were the original hackers. The hacker mindset really relates to people who can take things apart and make them better. There are even hackathons that have nothing to do with coding.
Alyssa Miller, a CISO with nearly two decades of experience in cybersecurity shared,
“Hackers are really creative folks who like to deconstruct things, figure out how they work, and make them all better. It’s all based on passion and wanting to see technology grow and improve.“
In other words, good hackers find creative ways with hacking testing to improve your startup’s technologies by finding its weaknesses and how to secure them.
Furthermore, it’s important to add that raising awareness about the pejorative use of the terms “hacker” and “hacking” throughout the media and popular culture is very important for the cybersecurity community. Hackers are often portrayed as villains in the media and pop culture when in reality, many of them are inherently good. Hackers and hacking is not synonymous with malicious adversaries or cybercriminals and their activities.
Black hat and white hat terms are now obsolete
In short, a black hat hacker, white hat hacker, and gray hat hacker all have differences. A black hat hacker once referred to a hacker who performs nefarious activities, a white hat hacker performs benevolent activities, and a gray hat hacker is somewhere in-between who will sometimes violate laws and ethical standards without the malicious intent of a “black hat” hacker. The terms black hat and white hat are now obsolete and discouraged from being used after being criticized as racially insensitive by communities of color and allies, especially after the GitHub controversy of using the terms “master” and “slave” in its repositories in 2020. Microsoft has sought alternatives in response. In addition, the terms blacklisting and whitelisting have also been criticized as inappropriate.
Listed below are alternatives to the terms black hat and white hat.
Black Hat Alternatives
- Attacker
- Malicious adversary
- Threat actor
- Cybercriminal
- Unethical hacker (bad)
White Hat Alternatives
- Security researcher
- Professional hacker
- Privacy researcher
- Whistleblower
- Hacktivist
- Ethical hacker (good)
The list of alternatives are straightforward, some of which have been proposed by the non-profit organization Hacking is NOT a Crime.
What is an Ethical Hacker?
An ethical hacker is a security expert who acts like a malicious intruder to penetrate networks, systems, or a system infrastructure in order to find and reveal their vulnerabilities to the system owners. They find security exposures in insecure system configurations, known and unknown hardware or software vulnerabilities, and operational weaknesses in process or technical countermeasures.
They help startups and organizations in a number of ways.
- Finding vulnerabilities and improving them
- Demonstrating tactics and techniques used by cybercriminals or threat actors
- Helping to prepare for a cyber attack
Ethical hackers are either directly employed by a startup or organization or can be Good Samaritans and participants of a Bug Bounty or a VDP program.

Ethical Hacking vs. Penetration Testing
Ethical hacking and penetration testing are very similar – the difference is that penetration testing narrowly focuses on specific parts of a network or web application, and ethical hacking focuses on overall security and includes penetration testing.
Penetration Testing
A penetration test, also known as a pen test, is an authorized simulated attack performed on a network, web application, mobile, hardware, or other component to evaluate its security. Penetration testers use the same tools, techniques, and processes as attackers to find and demonstrate the business impacts of weaknesses in a system. A few popular penetration testing tools are Nmap, MetaSploit, Hydra, and BurpSuite, to name a few. With the right scope, a pen test can dive into any aspect of a system.
The most popular types of penetration testing are:
- Network penetration testing
- Web application penetration testing
- Mobile application penetration testing
Network penetration testing
Network penetration testing targets a specific network or networks and focuses on the design, implementation, and maintenance of all hosts and services that are part of that network.
Web application penetration testing
A web application penetration is an assessment of the security of the code and use of software/libraries on which the application runs. Pen testers are security analysts that will look for vulnerabilities in a running web app such as:
- Injection vulnerabilities
- Broken authentication
- Broken authorization
- Improper error handling
In one of our previous articles, we discussed web application security risks. You can also learn how to secure web applications here.
Benefits of Penetration Tests
Penetration tests are excellent for discovering hidden flaws or vulnerabilities in your networks or web applications that you don’t want attackers to find, such as zero-day exploits. A penetration test is usually conducted in startups by an external company. This allows them to work on sensitive security issues in a limited group of people.
Network and web application penetration tests can help your startup:
- Find weaknesses in systems
- Prevent security incidents such as data breaches
- Determine the robustness of controls
- Support compliance with data privacy and security regulations (e.g., PCI DSS, HIPAA, GDPR)
- Provide qualitative and quantitative examples of current security posture and budget priorities for management
If you need any of the penetration testing services listed above, visit Zigrin Security Penetration Testing services page.
Responsible Vulnerability Disclosure Policy (VDP)
Responsible disclosure is a process that allows ethical hackers or security researchers to safely report found vulnerabilities in a startup or organization to their teams. A Vulnerability Disclosure Program (VDP) is a guideline or framework created by a startup or organization for security researchers to follow regarding the documentation and submission of vulnerabilities found. A VDP usually contains a program scope, a safe harbor clause, and remediation method, which is generally listed somewhere on an organization’s website. VDPs generally cover all publicly accessible, internet-facing assets but can be limited depending on the company’s resources.
More details on what a VDP usually contains are listed below:
- An introductory section that provides a background on the organization and its commitment to security.
- A safe harbor section that explicitly declares the organization’s commitment not to take legal action for security research activities that follow “a good faith” effort to follow the policy.
- Other guidelines that set further rules of engagement. For example, many vulnerability disclosure policies request that discovered exploits not be used to compromise data further, establish persistence in other areas, or move to other systems.
- A program scope that provides a clear view of the properties and systems covered by the policy, the products it may apply, and the appropriate vulnerability types. The scope should also include any testing methodologies which are not authorized.
- A process that includes the mechanisms used by ethical hackers to report vulnerabilities correctly. This section contains instructions on sending reports. It also consists of the information that the organization requires to find and analyze the exposure.
- A remediation method that explains to the security researcher what they can expect from the organization regarding their remediation process of vulnerabilities and bugs found. This usually includes deadlines of every stage of the disclosure process. There may be follow-ups to keep the security researcher up-to-date with their remediation plan.
- Rules of acknowledgement describing how the security researcher will be publicly acknowledged if desired.
- An option for anonymous submissions of vulnerabilities found may also be listed.
It is critical for security researchers to make sure that responsible disclosure is done in a proper manner to avoid unwanted lawsuits and potential criminal charges that can land them in prison. Navigating laws can be tricky, and it can be confusing and messy for security researchers to know what vulnerabilities they can and cannot disclose. If there is no VDP, Good Samaritan security researchers may have no easy way of responsibly disclosing vulnerabilities they find, which is problematic for the organization because those vulnerabilities will often go unreported and remain unfixed – a ticking time bomb just waiting for a cybercriminal to exploit them. Creating a responsible vulnerability disclosure policy (VDP) helps resolve any confusion and is essential for any startup or organization because it protects them from an attack or premature vulnerability release to the public that will endanger the organization.
Getting started with responsible disclosure simply requires a security page that states:
- What parts or sections of a site are within testing scope
- The types of bugs and vulns that are valid for submission
- A dedicated security email address to report the issue (often security@example.com)
To view an example of a VDP, visit Zigrin Security Vulnerability Disclosure Policy.
Guidance for Creating a VDP
For more guidance on creating a VDP, BugCrowd has created the Ultimate Guide to Vulnerability Disclosure here. You can also use the following tools to help you get started:
- BugCrowd’s open-source responsible disclosure policy: Allows any team at your startup or organization to conveniently create a VPD for free. It’s designed as a best practice guide for preparing and running a successful vulnerability disclosure program.
- NCSC’s Vulnerability Disclosure Toolkit: It contains the essential components you need to set up your own vulnerability disclosure process.
- Disclose.io’s policymaker: A “one-stop-shop” policy generator for anyone launching a vulnerability disclosure program (VDP) for the first time that is looking to update their VDP policy, or wanting to add features to an existing program.
Full Disclosure
Having a VDP is critical to clarify what a security researcher can or can’t do, and it protects a startup or organization. When a security researcher discovers a flaw in a startup or organization without a VDP, he or she is left with a few options:
- Ignore the discovery and not waste time on finding a way to communicate it with the company. That way a vulnerability keeps existing until someone else discovers it.
- Try to find a way to contact a security team within a company and disclose the vulnerability. This may often be difficult due to a lack of proper contact channels and a lack of basic security knowledge of the company’s support team.
- Publicly disclose the details of a vulnerability. This action is known as a full disclosure and is considered as the final way of getting the company’s attention about the problem.
A full disclosure of a vulnerability can be done by a security researcher if:
- They are unable to get in contact with the company
- Their vulnerability report was ignored (no reply or unhelpful response)
- Their vulnerability report was not fixed
- They felt notifying the public would prompt a fix
- They are afraid of legal prosecution
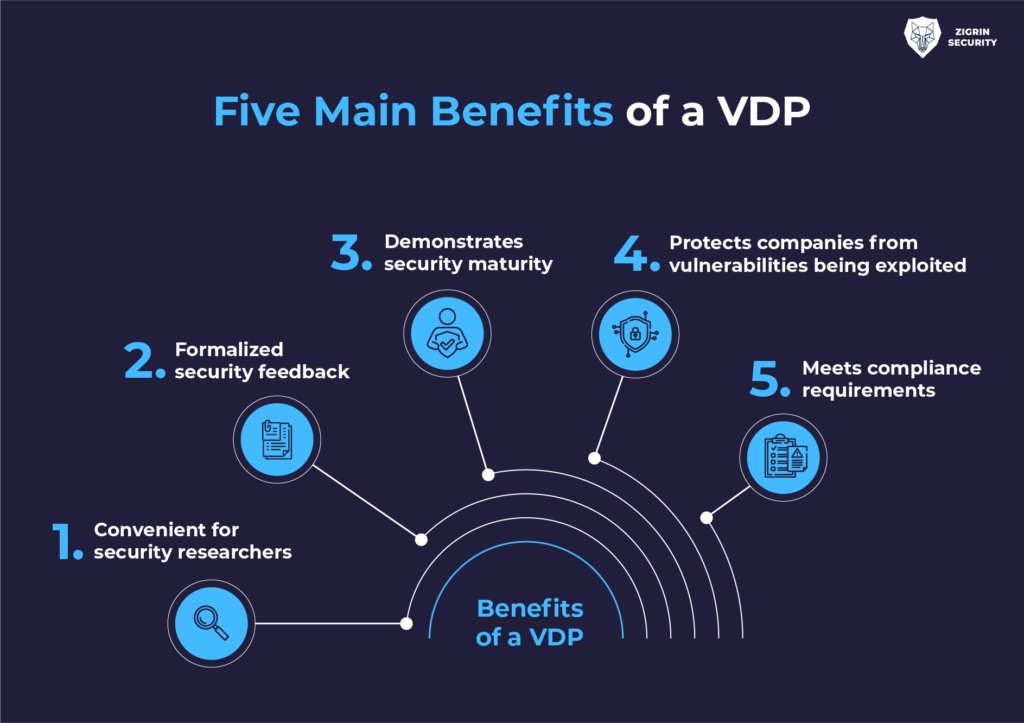
Five Main Benefits of a VDP
Having a Vulnerability Disclosure Program (VDP) is a win-win since it can boost cybersecurity for startups and organizations while benefiting security researchers for five main reasons:
1. Convenient for security researchers
- A Vulnerability Disclosure Program makes it easier for security researchers to report vulnerabilities directly to a startup or organization because a VDP provides clear guidelines on how they can be reported. It provides a scope which helps security researchers define what they can and cannot do, removing any confusion or concerns.
2. Protects companies from vulnerabilities being exploited
- A Vulnerability Disclosure Program boosts cybersecurity for startups and orgs because it encourages security researchers to report vulnerabilities before they are discovered by malicious actors and cybercriminals. Thus, a VDP gives startups and orgs an opportunity to remediate any vulnerabilities discovered by security researchers as quickly as possible.
3. Demonstrates security maturity
- A Vulnerability Disclosure Program demonstrates a company’s commitment to protecting its digital assets and responding to known risks. Not only that, but it builds confidence and trust in the brand.
4. Formalized security feedback
- Having a Vulnerability Disclosure Program in place provides the proper framework for engaging and maintaining a positive relationship with the security researcher community. It establishes and promotes more positive cooperation between internal and external parties when pertaining to vulnerabilities.
5. Meets compliance requirements
- It aligns cybersecurity programs with best practices, as defined by the US Government, NIST, DOJ, and others.
Disclosure Guidance for Security Researchers
It is beneficial for security researchers to have proper guidance in how they can disclose vulnerabilities, especially when many are fearful of legal repercussions or are unsure of how to responsibly disclose vulnerabilities they’ve found. When a VDP isn’t available, a security researcher can reach out to an organization and ask for a safe-harbor agreement before disclosing any vulnerabilities, but this increases the time before the fix and requires more work from the security researcher. Very often this means that the discovered vulnerability is not reported at all and stays unknown to the organization.
Safe-Harbor Agreement
A safe-harbor agreement allows you to report a vulnerability without any threat of legal action. A security researcher can withhold disclosure of vulnerabilities found in a company until a safe-harbor agreement is made for their protection. Companies may or may not agree to a safe-harbor agreement with security researchers. In cases when some do not, security researchers are strongly encouraged not to disclose the vulnerabilities they have found.
“It’s probably a good idea to get a lawyer if you can to review the safe-harbor agreement, and make sure there are no omissions where they can’t go after you.”
Alyssa Miller, CISO and author
Another safe way for a security researcher to disclose vulnerabilities is to make sure that the entity they’re researching has a robust Bug Bounty program, robust reporting procedures, and checking to see if there’s an informal history of how the business responds to inquiries and notifications in the past.
Bug Bounty Programs
A bug bounty is a monetary reward offered to an ethical hacker who successfully identifies a vulnerability or a security bug in a company’s web applications and networks. Bug Bounty programs allow companies to leverage the hacker community to enhance their security posture. These companies may have their Bug Bounty program listed on their website or a Bug Bounty platform that good hackers can publicly access. Some good hackers will hunt bugs occasionally, while others make a living from bug bounties earning full-time incomes.
Bug Bounty hackers are permitted to hack companies that participate in a Bug Bounty program under their discretion. It is an excellent way for ethical hackers to search for vulnerabilities and disclose them without fear of repercussions.
Usually, Bug Bounty programs often complement regular penetration testing and provide a way for organizations to test their applications’ security throughout their development life cycles.
Here is a list of Bug Bounty platforms:
Companies may disclose their bug bounties on their website like Microsoft, Apple, or Facebook, for example.
Summary
Recruiting good hackers who find hidden vulnerabilities before attackers can leverage security weaknesses are valuable as they help improve cybersecurity for startups. They aid in strengthening a startup’s security posture when implementing various security measures are simply not enough. These good hackers are ethical hackers, penetration testers, and bug bounty hackers or security researchers. In addition, having a vulnerability disclosure policy (VDP) is essential to a startup or company as it makes it easier for security researchers to report a vulnerability they identify, and it helps prevent unwanted lawsuits and prison time for security researchers, including full disclosures of exploits that can make companies vulnerable to attacks. Startups and companies that participate in Bug Bounty programs can greatly improve their security posture on a continuous basis by giving security researchers an opportunity to help their cybersecurity weaknesses, especially when incentives like monetary rewards are being offered. Good hackers are valuable to any startup or company and are worth rewarding.
If you would like to hire good hackers to conduct penetration testing of your product or network, contact Zigrin.
!The upcoming article in our series will explain what containerization is and describe the security benefits of containers.
Sources:
- https://krebsonsecurity.com/2021/06/how-does-one-get-hired-by-a-top-cybercrime-gang
- https://www.trendmicro.com/vinfo/us/security/definition/cybercriminals
- https://techstartups.com/2022/01/28/55-year-old-latvian-woman-mother-two-member-trickbot-cybercrime-gang-responsible-infecting-millions-computers-around-world
- https://www.techtarget.com/searchsecurity/definition/ethical-hacker
- https://www.synopsys.com/glossary/what-is-penetration-testing.html
- https://www.secjuice.com/hacking-is-not-a-crime-part-one
- https://www.secjuice.com/hacking-is-not-a-crime-part-2-how-security-researchers-can-responsibly-disclose-vulnerabilities/
- https://www.bugcrowd.com/resources/guides/ultimate-guide-to-vulnerability-disclosure
- https://www.securitymetrics.com/blog/do-you-need-web-application-penetration-test
- https://www.hackerone.com/vulnerability-management/what-are-bug-bounties-how-do-they-work-examples
- https://www.bugcrowd.com/glossary/vulnerability-disclosure-program-vdp

If you would like to hire good hackers to conduct penetration testing of your product or network
BOOK A CHAT WITH US
Is this article helpful to you? Share it with your friends.
Comment (1)
Comments are closed.


evden eve
December 21, 2022it’s awesome article. I look forward to the continuation.