Cybersecurity for startups – configure an edge security service
A security service edge (SSE), also known as SSE security or edge security, can bolster cybersecurity for startups by strengthening their defenses from cyber threats with its core services that follow the Zero Trust framework. An SSE is a product stack of components that serve as the security aspect of a secure access service edge (SASE), pronounced “sassy,” a cloud architecture model that combines network and security-as-a-service functions and delivers them as a single uniform cloud service. A SASE is an amalgamation of network services and security on a purpose-built cloud platform. However, the focal point of an SSE, or edge security, is simply what its acronym or name entails – security.
!This is the fourth out of eleven articles in the series “Cybersecurity for startups”. The previous one explains the details of modern frameworks for secure software development.
The Zero Trust security model
SSE security follows the Zero Trust security model, which abides by the motto, “Never trust, always verify,” and can strengthen cybersecurity for startups with its defense approach. According to the USA’s National Security Agency (NSA), the Zero Trust security model assumes a breach is inevitable or has already occurred. Therefore, it constantly limits access to only what is needed and looks for anomalous or malicious activity.
The Zero Trust security model offers more security and protection than the old standard of a castle-and-moat network security model, once believed to be a secure model where no one outside the network can access data on the inside, but everyone inside the network can. That belief shattered upon the realization there are inherent security flaws in the castle-and-moat security model. Those flaws can allow threat actors and insider attackers to take advantage of them and access data for nefarious reasons. Zero Trust is now the trusty choice for enterprises, governments, and cybersecurity for startups.

SSE security purposes
SSE security for startups allows them to enforce granular access controls and policies for employees to help mitigate risks as they access content that can be harmful on and off-network. It detects and mitigates cyber threats efficiently across the internet, web, and cloud services with capabilities. Those capabilities may include advanced threat prevention, Firewall-as-a-Service (FWaaS), malware detection, and remote browser isolation. Connecting and securing remote workers is another one of its use cases, which will continue to rise as the modern workforce continually adopts a work-from-home (WFH) policy. SSE security also enables you to find and control sensitive data no matter where it resides.
Most importantly, SSE security provides cybersecurity for startups by protecting them from these common threats.
Common threats SSE security protects startups from:
- Malware
- DDoS attacks
- Bots
- Phishing
- Etc
Anatomy of a Security Service Edge (SSE)
An SSE is a product stack of components that offers several capabilities and comprises three core services: a secure web gateway (SWG), cloud access security broker (CASB), and Zero Trust Network Access (ZTNA).
The three core services of SSE security are:
- Secure web gateway (SWG)
- Cloud access security broker (CASB)
- Zero Trust Network Access (ZTNA)
Other components include Firewall-as-a-Service (FWaaS), as well as remote browser isolation (RBI), and data loss protection (DLP) which may fall under a secure web gateway.

Secure Web Gateway (SWG)
SWG is a product that sits between end users (remote or in-office) and the internet, enforces granular use policies, and blocks access to or from malicious websites and links for threat and data protection. It acts as a “security gateway” by filtering unsafe web content and internet traffic at the application level to stop cyber threats and mitigate data breaches. An SWG is not to be confused with a proxy server that filters which connections are allowed, while a gateway doesn’t do any filtering. However, an SWG involves a proxy to enforce web category blocking and perform anti-virus capabilities.
SWGs may include the following technologies:
- URL filtering
- Anti-malware/anti-virus detection and blocking
- Remote browser isolation (RBI)
- Application control
- Data loss prevention (DLP)
- Content filtering
Configuring an SWG for URL Filtering
Below is a brief example of the configuration of a secure web gateway for managing URL filtering policies with the Comodo Secure Web Gateway product.
How to configure URL filtering policies with Comodo Secure Web Gateway:
1. Click ‘Configuration’ > ‘Web Content Policy’ > ‘URL Filtering’.
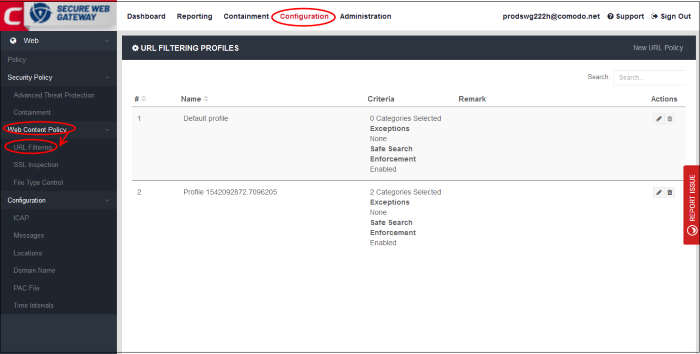
2. Enter the search parameters fully or partly in the ‘Search’ field to do one of the following:
- Create a new URL policy
- Edit an URL policy
- Delete a URL policy
3. Click ‘New URL Policy’ at the top-right.
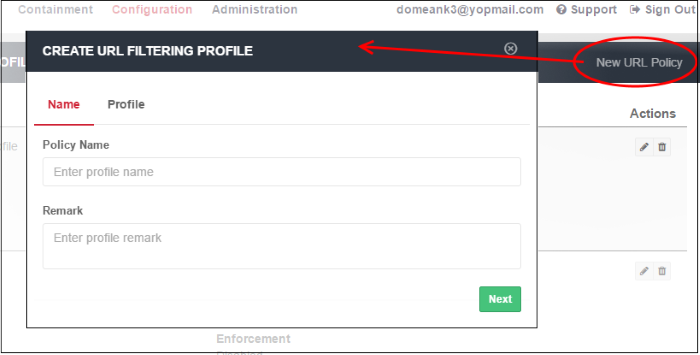
4. Create a label for the URL filtering profile (Policy Name).
5. Add helpful comments about the profile (Remark).
6. Click ‘Next’ or ‘Profile’ to specify the categories to block or allow.

7. You can select multiple categories (or ‘Select All’ for all of them) to block them at once. Review and deselect any of the categories you want to allow.
8. Click anywhere outside the drop-down to add your selected categories.

Remote Browser Isolation (RBI)
Remote browser isolation (RBI), also known as browser isolation for short, is one of the components of a secure web gateway that allows you to browse the web securely. It does this by physically isolating your local device from risks and cyber threats on the internet as you browse the web so that malware cannot affect your local endpoint device. Other features may include, to name a couple, URL filtering and multiple isolation mechanisms (E.g., rendering, session, process, and connection). Browser isolation in the cloud that uses a grid distributed, containerized architecture requires less server infrastructure than virtualization making it scalable and cost-efficient.
Several browser isolation platform products offer seamless installation into any cloud, virtual, or physical server allowing users to connect to the internet from any browser, for example, Google Chrome, Microsoft Edge, or Firefox, allowing users to begin browsing the web in a safe, secure manner. There may be an option to configure your local browser to push all traffic through the browser isolation platform, which can provide a native experience.
Five top browser isolation platforms are listed below (click links):
- Menlo Security
- WEBGAP
- Cloudflare
- Broadcom (formerly Symantec)
- ZScaler
Cloud Access Security Broker (CASB)
A CASB is an intermediary between users, devices, and cloud providers that enforces security policies. It is a company that helps protect third-party cloud-hosted services. Several technologies fall under the CASB umbrella and may be bundled together under one package. CASBs are a part of an SSE and also keep corporate Software-as-a-Service (SaaS), Infrastructure-as-a-Service (IaaS), and Platform-as-a-Service (PaaS) services safe from cyber threats and data breaches.
The top technologies of a CASB include but are not limited to:
- Shadow IT discovery
- Access control
- Data loss prevention (DLP)
Shadow IT discovery
Shadow IT refers to the unsanctioned use of software, hardware, or other systems and services. This unsanctioned use can occur at a startup or enterprise without the knowledge of its IT department. Two examples of Shadow IT are: 1) Using an unapproved tool to access, store, or share corporate data, or 2) accessing an approved tool without authorization.
The risks of Shadow IT are:
- Sensitive data may be compromised or stolen
- Organizations may unknowingly violate data compliance laws (E.g., GDPR laws.)
Access Control
Access control refers to a set of policies for restricting access to information, tools, and physical locations. Authentication and authorization are integral components of information access control in which software is used to authenticate and grant authorization to users who need to access digital information.
Real-world examples of physical access control include the following:
- Bar-room bouncers
- Subway turnstiles
- Airport customs agents
Examples of information access control include:
- Signing into a laptop using a password
- Unlocking a smartphone with a thumbprint scan
- Remotely accessing your boss’s internal network via a VPN
Data loss prevention (DLP)
Data loss prevention (DLP) ensures that users do not send sensitive or critical information outside a corporate or a startup’s network. DLP refers to software products that help an administrator control the data that users can transfer. Startups can adopt this to prevent insider threats and meet data privacy laws (E.g., GDPR), many of which have stringent data protection and access requirements.
Four Pillars of Cloud Access Security Brokers (CASBs)
The four pillars defined by Gartner are the foundational building blocks of any CASB solution. All pillars are required for CASBs to be effective and successful. The four pillars are:
- Visibility: CASBs help discover “shadow IT” that was not documented and may introduce unknown security risks.
- Data security: CASBs prevent confidential data from leaving company-controlled systems with the usage of access control and data loss prevention (DLP).
- Threat protection: CASBs block external threats and attacks and prevent data leaks by providing the following: Anti-malware detection, URL filtering, sandboxing, or even packet inspection.
- Compliance: It can be challenging for companies operating in the cloud to meet strict regulatory laws and requirements like the GDPR, SOC 2, or HIPAA. Some industries and regions that do not comply are at risk of penalties and fines. CASBs can help startups and enterprises implement security controls that meet regulatory standards and compliance.
Zero Trust Network Access (ZTNA)
ZTNA, also known as a software-defined perimeter (SDP), is a technology that implements a Zero Trust security model and enables secure access to internal applications for remote users. ZTNA gives remote users seamless, secure connectivity to private applications without ever placing them on the network or exposing apps to the internet.
ZTNA differs from virtual private networks (VPNs) by granting access only to specific services or applications as opposed to VPNs granting access to an entire network. When an employee at a startup utilizes a ZTNA, they can access specific applications or resources at their enterprise or startup, but only after being authenticated by the ZTNA service.
Once authenticated, the ZTNA then grants the user access to the specific application using a secure, encrypted tunnel which offers an extra layer of security protection by shielding applications and services from IP addresses that would otherwise be visible.
VPNs vs. ZTNA
VPNs used to work well for employees who needed to work remotely for temporary periods. However, after the mass adoption of the work-from-home (WFH) policy post-COVID-19, VPNs have lost their lackluster due to their lack of scalability, maintenance requirements, and costs.
Another issue that VPNs present is the attack surface they create. For example, a threat actor with the proper SSO credentials of an employee can log into a VPN and move laterally in the company’s network, providing them access to the company’s resources and data that the VPN was supposed to protect. This vulnerability presents problems as a security risk and threat.
ZTNA, on the other hand, secures user access such as that of an employee by granting access on the principle of least privilege. Rather than trusting based on correct credentials, Zero Trust authenticates only under the proper circumstances when the following details match up: the user, identity, device, and location.
Furthermore, ZTNA provides granular access rather than network access. Users are connected directly and securely to the applications and data they need, which prevents the possibility of lateral movement by malicious users. Plus, because user connections are direct, experiences are vastly improved when leveraging a ZTNA framework.
Cloud-Based Firewall-as-a-Service (FWaaS)
A firewall solution such as FWaaS delivered as a cloud-based service provides next-generation firewall (NGFW) capabilities such as advanced threat protection, web filtering, intrusion prevention system (IPS), and Domain Name System (DNS) security. It is similar to an onsite hardware firewall, except it offers scaling advantages allowing you to have new services provisioned due to being cloud-based. Additionally, an FWaaS is simple to deploy because all of its configuration details can be handled by an FWaaS provider’s team.
FWaaS provides the following features:
- Network monitoring
- Packet filtering
- Internet Protocol security (IPsec)
- Secure Sockets Layer Virtual Private Network (SSL VPN) support
- Internet Protocol (IP) mapping features
- Deep packet inspection (DPI) for identifying malware and alerting threat response teams to threats such as dangerous headers that appear innocent
- Machine-learning tools offered with some FWaaS solutions that include an NGFW identifies novel, zero-day threats by analyzing data packets for anomalous and potentially dangerous behavior
One of the key benefits of a FWaaS is, it allows the security posture of any enterprise or startup to migrate to a cloud infrastructure easily. Since it is cloud-based, updates and adjustments to settings are made without much hassle, freeing up a startup’s resources, time, and energy for high-priority projects and tasks. Its scalability and flexibility is another one of its attractive advantages.
Summary
SSE security, or edge security, is one of the best approaches to enable cybersecurity for startups because it is cloud-centric, modern (breaks away from traditional network security), and follows the most secure model, the Zero Trust security model. It allows security services to deliver in a unified way under one product stack or platform, which reduces risk and improves visibility. Since it uses the Zero Trust model, least-privilege access is enabled, providing secure connections between an employee (onsite or remote) and applications or resources, blocking threats from moving laterally. Applications are not externally facing the internet, which reduces risk and the attack surface. Its distributed architecture reduces latency and improves performance as a result. Many security services can be provided under one platform, reducing costs and offering simplicity as they are all unified. In summary, SSE security provides secure access to cloud services, detects and blocks threats, securely connects employees and remote workers, and identifies and protects sensitive data.
!The next article in the series will describe the functions of HTTP security headers and their implementation in different technologies.
Sources:
- https://www.cloudflare.com/learning/access-management/what-is-a-secure-web-gateway/
- https://www.zscaler.com/resources/security-terms-glossary/what-is-zero-trust-network-access
- https://www.zscaler.com/resources/security-terms-glossary/what-is-security-service-edge
- https://www.cloudflare.com/learning/access-management/what-is-a-casb/
- https://help.comodo.com/topic-436-1-842-10788-.html
- https://media.defense.gov/2021/Feb/25/2002588479/-1/-1/0/CSI_EMBRACING_ZT_SECURITY_MODEL_UOO115131-21.PDF
- https://www.gartner.com/en/information-technology/glossary/cloud-access-security-brokers-casbs
- https://www.fortinet.com/resources/cyberglossary/firewall-as-a-service-fwaas
- https://webgap.io/learning/the-webgap-approach.html
- https://www.zscaler.com/resources/security-terms-glossary/what-is-zero-trust-network-access

Let’s talk about securing your startup
Book a chat with a cybersecurity expert
Is this article helpful to you? Share it with your friends.

Comment (1)
Comments are closed.


Mae
January 3, 2023Hеllo thеrе, You have done an incredible job.
I wіll certainly digg it and personally recommend it to my
friends. I’m sure thеy’ll benefit from thіs website.