Cybersecurity for startups – backup user data and source code
Data backups are indispensable for a business continuity, disaster recovery, and incident response plan for cybersecurity for startups during disasters (e.g., fire and hurricane), human errors, and attacks such as ransomware. It is critical for startups to secure their data and ensure that sensitive data does not become lost by following best practices for data backups. One of the worst possible outcomes for a startup suffering from a data breach is irreversible damages caused by the loss of sensitive information, including intellectual property. Additionally, a startup that has lost all of its data due to a fire would be a nightmare situation.
A startup cannot return to normal operations in the event of a data loss, and financial losses can occur while operations are at a halt. A great strategy in place for backup security is imperative for a startup to ensure its survival in the event of physical and cyber disasters. For significant reasons, data backups are essential because they provide valid, uncorrupted data in the event of data loss or even data corruption.
Before getting into data backups, let’s have a quick overview of recovery sites.
!This is the seventh article in the series dedicated to the cybersecurity of startups. The previous one described security patches and the patch management process.
What are Recovery Sites?
Recovery sites are the location of restoration services for backup storage and are essential for recovery problems. They are onsite, offsite, or both. Depending on the types of recovery site needed, a startup may have a hot site, warm site, or a cold site during a disaster.
- Hot site: An environment fully set up and configured closely similar to a startup’s operating environment. It becomes operational immediately or within a few hours. It is the quickest recovery site.
- Warm site: A partially configured environment that contains the peripherals and software required to run, but it may not have expensive main processing computers needed. It becomes operational within a few days.
- Cold sites: An environment containing the basics or barebones for a startup to continue its operations. It may take weeks to become operational.

Four Primary Types of Data Backups
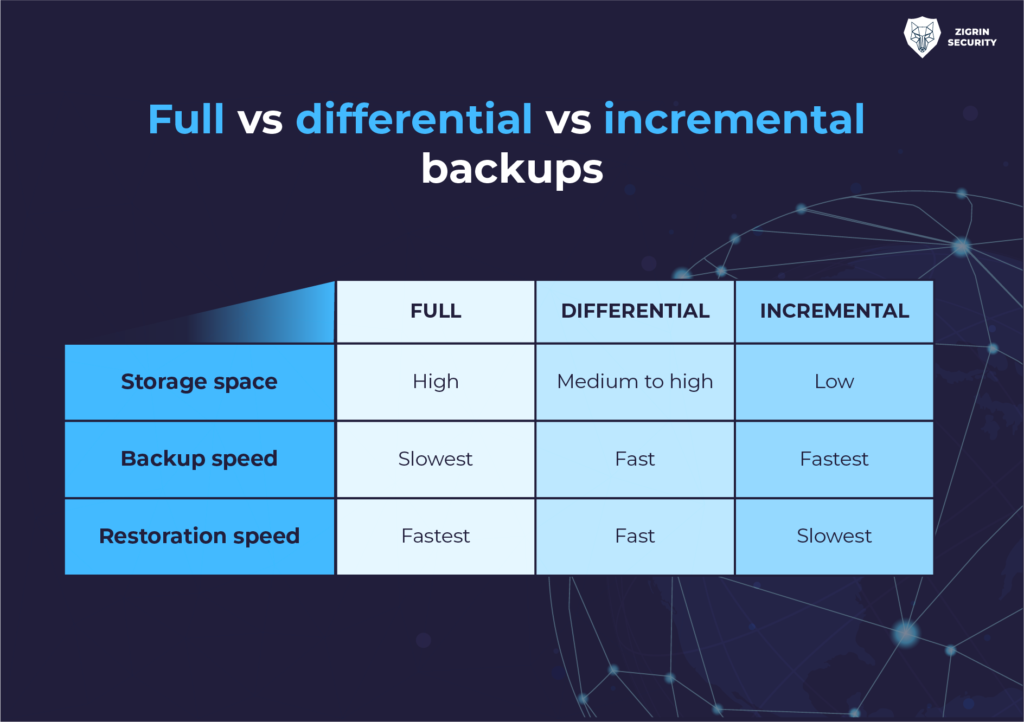
There are four primary types of data backups. They each have their own advantages and disadvantages. These data backups are:
- Full
- Incremental
- Differential
- Snapshots
Full Backup
A full backup is a complete copy of all files, directories, and software to a recovery site located onsite, offsite, or both. The advantage of this type of backup is the restoration of all data. Its disadvantage is the amount of time it takes to process. We know that it can take a while for those of us who had to make a full backup of our computer. Imagine how long it would take for a startup or mature organization to backup all data. There are scenarios when this may not be the best option when time is your number one enemy.
Incremental Backup
An incremental backup is similar to a differential backup because it relies on the last full backup completed, except it only backs up files that have changed since the last full or incremental backup occurred. As a result, it requires fewer files to back up. With incremental backups, less information becomes stored during each backup. The advantage of this type backup is that it requires less storage and time to complete. Its disadvantage is that the restoration process is a bit complicated and annoying. For example, in order to restore a system with an incremental backup, you must go to the last full backup and reload the system with that data. Then you have to update the system with every incremental backup ever done since the full backup.
Differential Backup
A differential backup will only backup files that have changed since the completion of the last full backup. It is dependent on the last time a full backup was completed. Consequently, a startup should decide the frequency of a full backup as part of its data backup strategy. The advantage of this type of backup is that the amount of time it takes for a differential backup is much less than a full backup. The disadvantages are restoration is slower than a full backup, backing up is slower than the incremental backup, and the storage space requirements are higher than for an incremental backup.
Snapshots
A snapshot is a backup copy of a virtual machine (VM) at a specific time. It copies the files that store the VM such as partitions, or memory. Its advantage is that it is so much easier to back up and restore files in a virtual machine than a physical machine because there is an option to revert to an earlier snapshot in time just by clicking a button. It is less time-consuming than waiting for a physical computer to restore itself. The disadvantages of snapshot backups are their reliance on a source database that must exist on the same server. A snapshot can run out of disk space, such as when many snapshot backups have occurred.
Source Code Must Be Backed Up Too
Data backups for startups don’t just include files and folders on systems – source code must get backed up too! Anything that is critical to your startup must get backed up, even if you don’t think they should. Imagine working on a GitHub project with your team at your startup, and the source code becomes eradicated after a malicious actor accessed it and breached your startup with a ransomware attack. To add insult to injury, because you did not back up your source code, hard work, and effort spent by your team on it is wasted away in the blink of an eye.
Consider the case of malicious actors or cybercriminals that wiped Git source code repositories and demanded a ransom payment in exchange for the source code. In 2019, at least a whopping 392 GitHub repositories were ransomed.
A cybercriminal may claim all source code has been downloaded and stored on one of their servers, and will give their victim 10 days to pay the ransom or make the code public. Here is an example of what a ransom note from a cybercriminal looks like:
To recover your lost code and avoid leaking it: |
Backup everything – that means your backups too!
It’s frightening to know that some ransomware groups target backups in their campaigns. The Federal Bureau of Investigation (FBI) and Cybersecurity and Infrastructure Security Agency (CISA) in the USA have even warned that malicious actors have added backup-specific tactics, such as encrypting or deleting system backups, to their arsenal—making restoration and recovery more difficult or infeasible for impacted organizations.
Protect Your GitHub with a Repository Backup Solution
Rewind is an effective repository backup and recovery solution and is the first step in protecting code in the cloud for GitHub, Bitbucket, and GitLab.
GitProtect has created a backup guide on how to protect GitHub, Bitbucket, and GitLab data and is accessible by download here.
11 Backup Best Practices for User Data
Following best practices for backing up user data is a smart strategy for backup security and boosting the security posture of your startup.
Here are 11 backup best practices to follow as a guideline:
- Create a backup policy and make sure your security policies include backups. Ensure every type of security policy in your startup applies directly to data backups and include backup-related systems within your startup’s scope. These policies can range from access control to physical security, and even to system monitoring and malware protection. Specify where backup data is to be located, who is authorized for performing backups, how to access files, how frequently backups must be done per policy, how data must be moved or format changed.
- Make sure your Disaster Recovery (DR) strategy includes backups. Include your data backup systems in your disaster recovery and incident response plans. Disasters such as ransomware attacks or natural disasters (e.g., a hurricane or tornado) can breach, compromise, or destroy your data backups. Have a plan to know how to respond to nightmare scenarios, such as when good data backups are adversely affected. Perform backups of digital data but consider digitizing physical documents because in a disaster like a flood, you want to have a copy of them.
- Automate your backups. Automating your backups ensures no files are missed, saves your team time from doing it manually, and makes it easier to perform backups on a regular schedule.
- Limit access rights to data backups. Assign backup access rights only to those authorized to handle the backup process for backing up files, software, and systems on the local network and in the cloud that provide backup access.
- Consider different backup locations. Store your backups offsite or at least in another building. A natural disaster, such as a hurricane, a fire, or a freak accident scenario can take out your data center and your backups in one take. Remember Murphy’s Law: Anything that can happen will happen. I’ve heard of nightmare stories of buildings spontaneously exploding due to chemical leaks no one detected. Don’t rule out the possibility of these unlikely disasters to occur.
- Limit physical access to data backups. Make sure physical access to backups are limited in facilities where you store your backups, even on backup servers, NAS, external drives or tapes. Handle your backup files as you would any other critical hardware. You might be able to validate this via SOC audit reports, independent security assessment reports or your own audits.
- Ensure backup media devices are protected. Some data backups get stored on portable drives, tapes, and related media. For these situations, use a fireproof and media-rated safe. Many so-called “fireproof” safes are misleading because they only protect paper rather than media. Media such as tapes, optical disks, and magnetic drives have a lower burning and melting point than paper. Make sure that a fireproof is also media-rated safe because a standard fireproof safe provides a false sense of security.
- Evaluate your vendors’ security measures. Discover what security measures your data center, cloud, and courier service providers are taking to ensure that backups remain safe in their hands. Ensure reasonable and consistent security measures are in place because good contacts that offer fallback measures are not enough.
- Ensure your network is secure. Store your data backups on a separate file system or cloud storage service on a physically or logically separated network. Unique login credentials outside an enterprise directory service are ideal for minimizing ransomware-related risks. Multi-factor authentication can add an additional layer of security in your backup environment.
- Prioritize backup encryption. Encrypt your backups whenever possible. Backup files and media must be encrypted, especially if they may get removed from onsite. Encryption implemented and managed in the right way serves as an excellent last layer of defense. It also helps provide peace of mind, knowing that the worst outcome is that your backup files have been lost or otherwise tainted but not accessed.
- Make comprehensive backups and test regularly. Back up your data repeatedly. Make sure you backup everything that’s important first, including the data in your network and cloud. Test your backups even when you’re not getting any errors on them. There’s nothing worse than attempting to recover from a loss, only to find out your backups are either not legitimate, you’ve backed up the wrong data, or even worse, no data at all.

Six Best Data Backup Solutions for Small Startups
Data backup solutions can help boost backup security for startups. The six best data backup solutions for small startups are listed below.
Legal Implications
When choosing a storage location for backups, startups must consider the legal implications of cloud storage for backups. Different jurisdictions have different laws, rules, and regulations concerning things like encryption. Knowing legal implications of how data backup storage plans can be affected is critical to prevent any downstream problems.
Data Protection Solutions
Data protection laws play a prominent role in cybersecurity for startups. Data protection and privacy laws strengthen individual control over how startups and organizations use personal data.
A few long-standing industry regulations include:
- Payment Card Industry Data Security Standard (PCI DSS)
- Health Insurance Portability and Accountability Act (HIPAA)
- Gramm-Leach-Bliley Act (GLBA)
Government regulations include the following examples:
- General Data Protection Regulation (GDPR) in the EU
- Data Protection Act in the UK
- California Consumer Privacy Act (CCPA) and California Privacy Rights Act (CPRA) in the US
Non-compliance with these regulations will negatively impact a startup or organization, such as severe penalties and fines, damage of reputation and loss of trust, and legal action and its associated costs.
Data protection solutions can help mitigate against non-compliance. There are data protection solution softwares that a startup can use.
The top 10 data protection solution software are:
- Acronis Cyber Protect
- CybeReady
- Barracuda Backup
- Cohesity DataProtect
- Eperi
- Hitachi Vantara Data Protection Suite
- Spectral
- Storagepipe Multiplatform Backup
- Thales Data Protection on Demand
- Polar security
Summary
Data backups are vital for the survival of a startup and backup security, such as the protection of sensitive data including intellectual property. All data that is important must be backed up including source code. A startup cannot return to its normal operations when critical data is lost, especially in the case of a ransomware attack when malicious actors encrypt all data and destroy them. It is imperative to have a data backup strategy in place for business continuity, disaster recovery, and incident response plans. In addition, awareness of legal implications of data backups are important too. A robust data backup strategy will certainly boost cybersecurity for startups and protect them from unwarranted natural and cyber disasters that can wreak havoc and cause irreversible damage forcing a startup to completely cease business operations.
!The article was dedicated to backup security and data protection solutions. The next one will highlight the importance of centralizing logs and logging best practices.
Sources:
- https://www.darkreading.com/dr-tech/a-comprehensive-backup-strategy-includes-saas-data-source-code
- https://www.darkreading.com/dr-tech/source-code-security-the-case-for-making-backups
- https://www.zdnet.com/article/a-hacker-is-wiping-git-repositories-and-asking-for-a-ransom/
- https://gitprotect.io/git-backup-guide.html
- https://www.usgs.gov/data-management/backup-secure
- https://www.backup4all.com/differential-backup-kb.html
- https://www.techtarget.com/searchdatabackup/tip/Ten-ways-you-can-make-your-data-backups-more-secure
- https://www.eiresystems.com/best-cloud-backup-solutions-for-small-businesses/
- https://www.pcmag.com/picks/the-best-cloud-backup-services-for-business
- https://cybeready.com/top-10-data-protection-software
Is this article helpful to you? Share it with your friends.

